Don’t know what phishing messages are? Discover how to spot and avoid the dangers of these scam emails with our essential guide.
What Is a Phishing (and Scam) Email?
Phishing messages are false emails that deceive the recipients into exposing their personal and financial secrets. Some of these emails pretend to be from genuine sources like banks, social media websites or even acquaintances and friends thus appearing as if they can be trusted. They aim at stealing identities, accessing private accounts or directly drawing funds out of innocent victims.
In addition to seeking personal data, these scam emails go further by attempting to load malware onto the recipient’s computer or deceive them into taking part in fraudulent activities. They capitalize on this trust through techniques such as customized salutations, spoofed email addresses and manipulated hyperlinks, which seem real at first sight. It takes a sharp eye for detail and a recognition of subtle hints betraying ill intentions to detect such mail messages.
How to Identify a Phishing Email?
Being able to identify a scam email among the many daily communications can be tough, but it is important for safeguarding your personal and financial details.
While phishing attempts have become more sophisticated over time, there are several red flags that can enable you to recognize such deceptive messages:
1. Suspicious Sender Addresses
One of the first defense lines against phishing lies in checking the email address of the sender. Phishers often use addresses that look like legitimate ones with small differences, which may not be seen at first sight.
For example: an email pretending to come from a well-known firm might be sent from a website that contains one letter in incorrectly spelled or different domain name extensions. Always compare the sender’s e-mail address with previous correspondences from the same institution.
2. Mistakes in Grammar and Spelling
Genuine firms usually check their messages for correct grammar and spelling. Conversely, these errors might originate from either professional scammers unwilling to evade spam filters or less intelligent swindlers whose English is not native language used on those emails. Due to this, they intentionally make mistakes which can range from simple spellings errors they made to difficult sentence constructions.
3. Unsolicited Attachments or Links
In many instances, a phishing message will contain attachments or links that you are compelled by the sender to open or click on. These may take you to malware-infected sites or other websites that are designed to steal your information.
A piece of advice: do not trust any email that tells you to download an attachment or click on a link if it wasn’t expected. Most companies would refer you directly to their official website instead of asking for action via an email.
4, Too Good to Be True Offers
In case an electronic mail offers something too good to be true like a considerable amount of money, surprising award or unbelievable price reductions, then most likely it is a fraudulent message. Such offers are employed by fraudsters as means for luring gullible users into sharing their personal data or even transferring funds.
5. Urgent or Threatening Language
Urgency and threats are some of the techniques that phishers use to make people act fast. This may involve information that your account will be closed, legal consequences, or other actions if you fail to act. Legitimate companies don’t engage in this kind of pushing.
How to Stop Phishing Emails?
A multifaceted approach is necessary to block phishing emails from entering your inbox, which includes vigilance, technology and proactive measures.
As hackers become more sophisticated in their attacks, our strategies for defending against them must also evolve. Here’s how you can protect yourself from these devious tactics:
1. Use WOT’s Mail Protection
Advanced security solutions like WOT’s Mail Protection can greatly enhance your email security. This feature notifies you when an email contains a suspicious link or untrusted attachment right within your email client adding another layer of protection in the process.
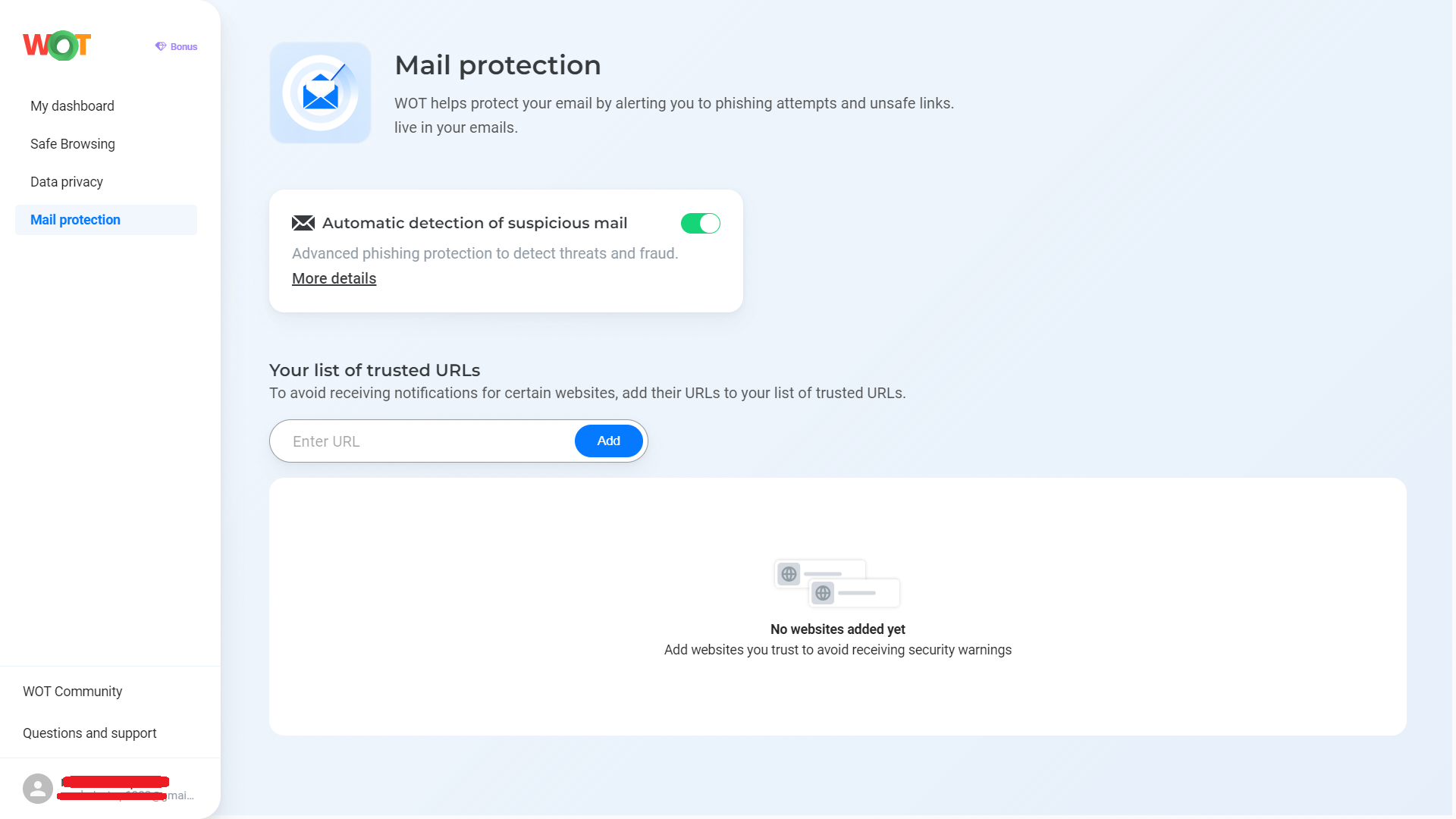
Enabling Automatic Detection of Suspicious Mail offers you a complete anti-phishing solution by WOT that proactively detects and warns against threats prior to their execution. Moreover, adding trustworthy URLs to your whitelist ensures you receive notification only when truly suspicious activities occur thereby lowering the risk of missing out on a dangerous email.
Experience worry-free browsing and emailing with WOT’s protection
2. Be Suspicious of Unsolicited Requests
Being skeptical goes a long way in preventing oneself from falling victim to phishing. Always handle any unsolicited request for personal or financial information with caution. Legit organizations hardly demand sensitive information via email. In case you get any such request, it is important that you confirm its authenticity by directly contacting the organization using verified contact details.
3. Use Email Filters
Many email providers have filters installed in their systems that help identify and separate spam and potential phishing emails. By configuring these filters according to your needs, the number of phishing attempts reaching your inbox can be dramatically reduced. Regularly check your spam folder so that legitimate mails are not misclassified and adjust your filter settings accordingly.
4. Regular Software Updates
It is important to keep your operating system software, web browsers and security software up-to-date at all times. Phishers often take advantage of security vulnerabilities addressed by software updates to infiltrate systems. To be in line with the latest threats, it would be imperative that automatic updates are enabled where possible.
5. Self-Educate (and Teach Others)
Knowledge works best against phishing scams than anything else does. Read about the latest ways used by phishers, as well as tales behind this malpractice so that those near you out there can also learn about them. This greatly reduces the chances of success associated with those who practice such acts of forgery.
6. Verify Links and Attachments
Before clicking on any link or downloading an attachment, take a few seconds to think about its safety. Hover over links to see the address they point at and check for discrepancies. If unsure, type the website’s address directly into your browser instead of clicking on a link. Be cautious with email attachments as well, especially if they come from unknown senders. In case of doubt, contact the sender via alternative methods apart from emails in order to ascertain the legitimacy of such mail.
7. Enable Two-Factor Authentication (2FA)
So what is 2FA and what does it do? This security feature 2FA, when enabled on your accounts, makes it more difficult for attackers to gain full access even after successful phishing attacks. With this functionality, logging into an account requires not only entering a password but also using another piece of information like phone validation code among others. This significantly decreases the probability of unauthorized access.
8. Monitor Your Accounts Regularly
Keep monitoring all financial and personal accounts regularly so that any abnormal activity can be detected early enough. As soon as possible, identifying unauthorized transactions can have key implications toward mitigating further losses. A majority of banks offer unusual account activity alerts that are effective in detecting fraud cases before they actually happen.
How to Report Phishing Emails?
Phishing emails must be reported in the fight against cyber crime so as to protect yourself and other people. That means you play a role in reducing the impact and prevalence of phishing attacks by exposing these deceptive messages. Below are way on how you can report phishing emails effectively:
1. Utilize the In-Built Email Reporting Features
Most email platforms like Gmail and Outlook have functionality that enables users to report phishing attempts directly from within their inboxes. This not only assists in improving an email provider’s filtering algorithms but also alerts them to new tactics used by phishers.
To report a phishing email, one would usually need to select the message then locate either a “report” or “spam” button. By clicking this button, it prompts you to identify whether it is such an attempt or not. Besides, this leads to shifting the corresponding mail into your spam folder hence reporting the sender to the service provider.
2. Tell the Company Being Impersonated
If a specific company has been impersonated by a phishing email, it is good if you could notify those affected about this incident. Majority of companies have avenues for reporting cases where individuals pretend to be associated with them and intend to defraud others via illegal online schemes. This can typically be done on their official site. Consequently, notifying them helps them take action against scammers and protect their clients.
3. Report to Cybercrime Agencies
There are several government institutions across various countries globally that are responsible for dealing with cybercrimes such as phishing:
- The Federal Trade Commission (FTC), for example, allows American citizens who have received malicious emails purporting to be forms of fraudulence contact it on its official website.
- The Anti-Phishing Working Group (APWG), on other hand, provides channels through which information relating to internet-based frauds of this nature can be passed along thereby assisting authorities with evidence necessary for enforcement actions targeting suspicious websites or emails. This helps in tracking and minimizing phishing activities.
4. Educate Your Network
Informing people about your personal experience regarding such acts of fraudulence can act as a way of indirectly reporting phishing scams. This prevents others from being deceived. Sharing information about cyber criminals trying to steal their information through social media or other means raises awareness on what to look out for among those in contact with you.
5. Forward to Specialized Email Addresses
There exist some organizations and email providers which have got special email addresses where you can forward any emails that appear to be phishing attempts for further analysis. For example, forwarding it to the address given by the Cybersecurity and Infrastructure Security Agency (CISA) contributes towards their cybersecurity defense efforts. Such data may also be analyzed so as to find ways of countering them.
The Final Reel-In
The Internet Crime Report by the FBI’s Internet Crime Complaint Center (IC3) has been released and just like last year, phishing was again the most commonly reported crime in 2023. In the war against phishing emails, intelligence and attentiveness are your best weapons. By recognizing the tricks that fraudsters use and having effective measures like WOT’s Mail Protection, you can cut down significantly on this danger of being trapped by these deceitful schemes.
Phishing attempts are constantly changing; thus, it is important to stay updated about current scams and ways to protect yourself from them. Let us be vigilant, question the genuineness of unexpected appeals and utilize available technologies to safeguard our personal data from prying eyes. Unitedly, we can outmaneuver phishing attacks and keep our digital lives safe.
FAQs
How to tell if an email is phishing in Gmail?
Gmail has its own mechanisms that identify suspicious emails, often relegating them to spam or issuing warnings about potential phishing. However, one may check for the sender’s email address, unexpected requests for personal information and links/attachments coming from trustworthy sources among the contacts. Gmail is continually updating its security to fight new techniques of phishing; hence any alerts or alarm received will be crucial.
What should I do if I accidentally clicked a link in a phishing message?
It is important to act quickly once you have clicked a link in a phishing email so as to reduce risk. Firstly, change passwords for all accounts which might be tampered with – especially when one uses the same password on multiple sites. This can be done by activating two-factor authentication just to improve security. Also run anti-virus software on your computer as this will detect any malware present. Verify unusual activities that could possibly be identity theft through your financial statements and credit reports.
How do I know whether an email is a phishing scam or if it’s authentic?
Phishing messages have numerous signs that help in differentiating them from real ones. Examples of such signs include greetings like “hi there”, misspelling words and grammar errors, and requests for sensitive details like passwords and bank account numbers. Legitimate companies typically do not ask customers about their private information using electronic mails. Furthermore, senders who claim to be from company A can also be checked their genuineness via official channels instead of replying back through such e-mails or making calls using contact given here.
Can my PC get infected by a phishing email without clicking anything?
Opening up a phish email alone does not result in computer contamination. However, downloading attachments or clicking links within the mail can expose your system to malware. Nevertheless, modern mail clients provide features that protect against automatic downloads but still it is better to be careful when handling such dangerous messages. Update your antivirus regularly to have it guard you from any possible risks.
What are the common types of phishing?
Many techniques and approaches are used in phishing attacks, which target different information types. Among them are emails pretending to originate from banks and requesting customers’ account details, false social network alerts requiring some actions, or a message looking like coming from a friend but containing harmful links or asking for confidential data. Others include scam invoices, fraudulent tax refunds, and charity scams often targeted at natural calamities or holidays. Such knowledge increases your chances of avoiding such scams.
